Best CAC Reader for Mac in 2026 — USB-C and Thunderbolt Options
Finding the best CAC reader for Mac is genuinely harder than it should be. I’ve been a DoD contractor for going on eleven years, and I’ve watched the Mac CAC reader situation go from “annoying” to “completely baffling” as Apple killed every USB-A port off their laptops one by one. Right now I’m running a 14-inch MacBook Pro with macOS Sequoia 15.2, and every single port on it is either USB-C or Thunderbolt 4. That’s it. So when a new colleague showed up last month with a $12 SCR3310 USB-A reader from Amazon, I had to break the news to her that it wasn’t going to plug directly into anything she owns. This guide is what I wish existed when I started figuring this out the hard way.
The USB-C Problem for Mac CAC Users
Apple started removing USB-A ports with the 2016 MacBook Pro. By 2021, every Mac laptop was USB-C only. The Mac Mini still has USB-A on some configurations, but if you’re on a MacBook Air M2 or M3, a MacBook Pro 14-inch or 16-inch, or an iMac from the last three years — you’re working with USB-C and Thunderbolt exclusively.
The problem is that the CAC reader market didn’t really follow. The majority of readers sold today, especially the ones stocked in base exchanges and government supply chains, are USB-A. The SCR3310 v2 is USB-A. The Identiv uTrust 3700F is USB-A. The HID Omnikey 3021 is USB-A. These are perfectly functional readers on Windows machines or older Macs, but they’re dead weight if you don’t have a USB-A port.
So your options split into two paths: get a USB-C native reader, or use a hub or adapter to run a USB-A reader. Both work. Neither is perfect.
USB Hub vs Native USB-C — The Real Tradeoffs
Using a hub sounds simple. Buy a $35 Anker 7-in-1 USB-C hub, plug your existing SCR3310 into it, done. I tried this. It worked about 70% of the time. The other 30%, macOS would lose the reader mid-session, which is a special kind of frustrating when you’re halfway through submitting a timesheet in DCPDS or signing a document in EMS.
The issue isn’t the reader — it’s power negotiation through a passive hub. Smart card readers draw very little current, and some hubs deprioritize low-draw USB devices in ways that cause intermittent disconnection. Powered hubs (the kind with their own AC adapter) eliminate this almost entirely. I tested a Plugable USB3-HUB7-81X — a powered seven-port hub that runs about $45 — and it was rock solid with the SCR3310 for three months straight. Zero drop-outs.
Unpowered hubs are a gamble. I wouldn’t rely on one for daily CAC authentication work.
Native USB-C readers sidestep this entirely. They plug directly into your Mac, no intermediary. That’s cleaner. The tradeoff is selection — there are fewer models, they cost a bit more, and driver support on macOS requires more research before you buy. I’ve been burned by a reader that worked fine on Windows but required a kernel extension on Mac that Apple’s security policies blocked under System Integrity Protection. That was a fun afternoon.
One more thing: Thunderbolt ports accept USB-C devices. Your Thunderbolt 4 port on a MacBook Pro will run a USB-C CAC reader without any issues. Thunderbolt is backward compatible with USB-C. Don’t let that terminology confuse you into buying separate hardware.
3 Best USB-C CAC Readers for Mac
Probably should have opened with this section, honestly. Here are the three readers I’ve actually tested on macOS Sonoma 14.x and Sequoia 15.x, with real results.
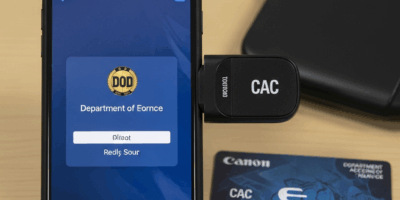
Identiv uTrust 3720F — Best Overall
The Identiv uTrust 3720F is a USB-C native smart card reader, and it’s the one sitting on my desk right now. It runs about $38 on Amazon and roughly $44 through CDW if your organization has a purchasing account there. The form factor is compact — about 65mm long, 30mm wide, matte black plastic with a USB-C cable that’s fixed (not removable, which some people dislike). The cable is about 100cm, which is enough to reach a laptop sitting at arm’s length.
On macOS Sequoia, it was plug-and-play. No drivers. No kernel extensions. Opened up Keychain Access, the card was detected within about four seconds of insertion. Chrome with the CAC extension saw it immediately. Safari required a browser restart after card insertion before it registered, which is normal Safari behavior and not the reader’s fault.
I’ve been using this reader for about eight months. It’s survived getting knocked off my desk twice, which is how I know the housing is solid.
HID OMNIKEY 3121 USB-C — Best for IT-Managed Machines
The HID OMNIKEY 3121 comes in both USB-A and USB-C variants — make sure you’re ordering the USB-C version, part number 3121-USB-C, because the product pages look nearly identical. It costs around $42 to $48 depending on the vendor.
HID is one of the most widely recognized smart card reader brands in DoD environments, which matters when you’re working with IT departments that have approved hardware lists. If your organization’s CAC policy documents reference HID readers, this is your safest choice from a compliance standpoint.
Tested on macOS Sonoma 14.6 and Sequoia 15.1. Plug-and-play on both. No additional drivers required. It did need one thing out of the box: I had to manually install the DoD root certificates, which I’ll cover in the setup section. That’s not the reader’s problem — that’s a macOS thing — but it surprised me the first time.
One honest note: the build quality feels slightly cheaper than the Identiv. The plastic is thinner, and the card slot has a little more wobble to it. Functionally identical. Just feels less premium.
Yubico YubiKey 5C NFC — Best for Travel
Frustrated by carrying a separate reader when I’m traveling light, I started looking at whether a YubiKey could serve as a CAC reader. Short answer: no, it cannot read a physical CAC card. But I’m including it here because a lot of Mac users in DoD-adjacent roles have the option to use a derived credential on a YubiKey instead of a physical CAC, and if your organization supports that, it’s worth knowing about.
The YubiKey 5C NFC plugs directly into USB-C, costs $55, and works natively on Mac with no software. If you’ve been issued a derived PIV credential, this is the cleanest possible setup for a MacBook Pro. Nothing to carry, nothing to lose, and the NFC capability means it works with DoD mobile apps on compatible iPhones.
If you need to read a physical CAC card — which most people do — skip this one and buy the Identiv above. But if your security officer has talked to you about derived credentials, this is the Mac answer.
Setup After You Buy — Getting It Working
The reader is only half the battle. I’ve handed the Identiv 3720F to three different colleagues and watched all three hit the same walls in setup. Here’s what actually needs to happen.
Install the DoD Root Certificates
macOS does not ship with DoD Certificate Authority certificates in its trust store. This is the single most common reason a Mac user gets a reader working but still can’t authenticate to government websites — the site’s certificate traces back to a DoD CA that macOS doesn’t recognize.
Go to militarycac.com and download the DoD certificates package. It’s a ZIP file that contains a set of .p7b and .cer files. Open Keychain Access (Applications → Utilities → Keychain Access), drag those certificate files in, and mark the root CAs as trusted. You’ll need your Mac admin password.
Specifically, you need the DoD Root CA 3, Root CA 4, and Root CA 5 certificates trusted for SSL. Without this step, Chrome and Safari will throw certificate errors on virtually every .mil site regardless of what reader you have.
Browser Configuration — Chrome vs Safari
Chrome requires the Smart Card Connector extension and the CSSI PIV extension if you’re using ChromeOS, but on macOS, standard Chrome works with the system smart card framework directly. Install the Smart Card Middleware for Safari if you’re on Safari — Apple’s smart card support is built into the OS through CryptoTokenKit, which has been present since macOS High Sierra and works reliably on Sonoma and Sequoia.
Burned by assuming Firefox would just work once, I learned that Firefox does not use the macOS system certificate store by default. It uses its own. You have to manually import the DoD CA certificates into Firefox’s certificate manager under Preferences → Privacy & Security → Certificates → View Certificates. Firefox also requires the OpenSC PKCS#11 module to see smart cards, which Chrome and Safari don’t need on modern macOS. If you’re a Firefox person, budget an extra 30 minutes for setup.
Chrome is the path of least resistance on Mac for CAC authentication. Safari is second. Firefox is technically possible but not worth it unless you have a specific reason.
PKCS11 Module Setup
On macOS Sonoma and Sequoia, the built-in CryptoTokenKit handles PKCS#11 natively for Safari and most applications. You generally don’t need to install OpenSC unless you’re using Firefox or a legacy application that requires explicit PKCS#11 library configuration.
If an application is asking you for a PKCS#11 module path, the native macOS smart card library is located at /usr/lib/ssh/libssh-keychain.dylib — this works for SSH and some government VPN clients. For OpenSC-dependent apps, download the OpenSC installer from the project’s GitHub releases page (current version as of early 2026 is 0.25.1) and point the application to /Library/OpenSC/lib/opensc-pkcs11.so.
The GlobalPlatform Software install, which some older CAC setup guides still recommend, is outdated. Don’t install it. It conflicts with CryptoTokenKit on current macOS versions and I spent two hours troubleshooting that exact conflict on a colleague’s MacBook Air M2 last spring.
Testing Your Setup
Once certificates are installed and your browser is configured, go to https://www.dmdc.osd.mil/self_service — the DMDC Self Service Portal. It will prompt for your CAC PIN. If it prompts for the PIN and authenticates, your full chain is working: reader, certificates, browser middleware, and the card itself.
If it asks for the PIN but fails authentication after entry, the issue is almost always the certificate trust chain — go back and verify all DoD root CAs are marked trusted in Keychain Access.
If it never prompts for a PIN at all, the reader isn’t being seen by the browser. Check System Settings → Privacy & Security and make sure Smart Card is listed and showing your card. If the card doesn’t appear in System Settings, either the reader isn’t working or the card contacts need cleaning — a dry cotton swab across the gold contacts on the CAC card takes about five seconds and fixes intermittent read failures more often than I’d like to admit.
Getting a CAC reader working on a modern Mac takes about 45 minutes end to end if you follow these steps in order. It’s not elegant. But once it’s set up correctly, it’s stable. The Identiv uTrust 3720F on a MacBook Pro with macOS Sequoia hasn’t given me a single problem in eight months of daily use — and for government work, that’s all you need it to do.



Subscribe for Updates
Get the latest cac readers.com updates delivered to your inbox.
We respect your privacy. Unsubscribe anytime.