Setting up CAC readers on Linux has gotten complicated with all the different distros and package managers flying around. As someone who’s been running Linux as my daily driver since the early Fedora Core days and had to make DoD sites work on it, I learned everything there is to know about getting your CAC authenticated on a Linux box. Today, I will share it all with you.
What You Need Before Starting
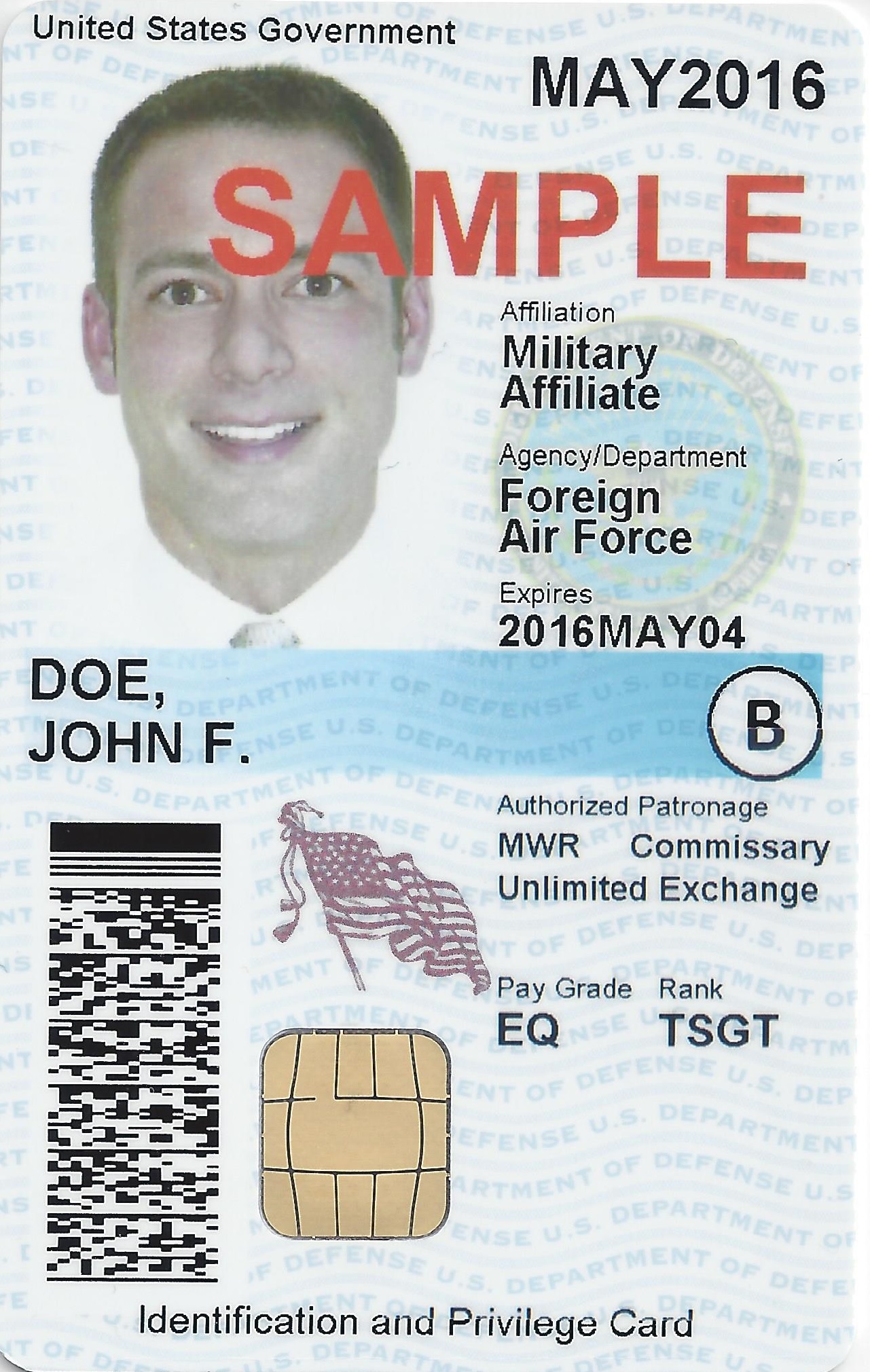
Before you touch anything, make sure you’ve got a USB CAC reader (most common models work fine on Linux), your actual CAC card and PIN, sudo access on your box, and either Firefox or Chrome installed. If you’re on a locked-down government Linux machine, you might need to coordinate with your admin for some of these steps.
Ubuntu Setup (20.04 / 22.04 / 24.04)
Ubuntu is probably the most common Linux distro people try to use with a CAC, so let’s start here.
Install the packages
sudo apt update
sudo apt install pcscd pcsc-tools opensc opensc-pkcs11 libpam-pkcs11 libnss3-toolsFire up the smart card daemon
sudo systemctl start pcscd
sudo systemctl enable pcscdThat second command makes sure pcscd starts automatically on boot. Don’t skip it — you’ll forget later and wonder why your reader stopped working after a reboot.
Verify your reader is detected
Plug in your reader, insert your CAC, and run:
pcsc_scanYou should see your reader model and some card ATR data scroll by. Hit Ctrl+C to get out. If nothing shows up, try a different USB port or check lsusb to make sure the hardware is even recognized.
Get the DoD certificates installed
wget https://dl.dod.cyber.mil/wp-content/uploads/pki-pke/zip/certificates_pkcs7_DoD.zip
unzip certificates_pkcs7_DoD.zip
cd certificates_pkcs7_DoD
for cert in *.p7b; do
openssl pkcs7 -inform DER -in "$cert" -print_certs -out "${cert%.p7b}.pem"
done
sudo cp *.pem /usr/local/share/ca-certificates/
sudo update-ca-certificatesThat for loop converts the PKCS7 bundles into PEM format that Linux can actually use. It looks complicated but it’s just a batch conversion.
Configure Firefox
Open Firefox, go to Settings, then Privacy & Security. Scroll down to Security Devices and click it. Hit “Load,” name it something like “CAC Module,” and point the module filename to:
/usr/lib/x86_64-linux-gnu/opensc-pkcs11.soClick OK and you should be able to hit DoD sites that need your CAC.
Fedora Setup (38 / 39 / 40)
Fedora uses dnf instead of apt, and some paths are different, but the concept is identical.
sudo dnf install pcsc-lite pcsc-tools opensc nss-tools
sudo systemctl start pcscd
sudo systemctl enable pcscdFor certs, same download process as Ubuntu but drop them in a different location:
sudo cp *.pem /etc/pki/ca-trust/source/anchors/
sudo update-ca-trustFirefox module path on Fedora is /usr/lib64/opensc-pkcs11.so — note the lib64 instead of lib/x86_64-linux-gnu.
RHEL Setup (8 / 9)
Probably should have led with this section, honestly, since RHEL is what most government Linux deployments actually run. You might need to enable an extra repo first:
sudo subscription-manager repos --enable codeready-builder-for-rhel-9-x86_64-rpms
sudo dnf install pcsc-lite pcsc-tools opensc nss-tools
sudo systemctl start pcscd
sudo systemctl enable pcscdCertificate path is the same as Fedora: /etc/pki/ca-trust/source/anchors/ followed by sudo update-ca-trust extract. Firefox module path is also /usr/lib64/opensc-pkcs11.so.
Chrome/Chromium Config
That’s what makes the NSS database approach endearing to us Chrome users on Linux — you configure it once from the command line and it just works.
modutil -dbdir sql:$HOME/.pki/nssdb -add "CAC Module" -libfile /usr/lib64/opensc-pkcs11.soRestart Chrome after running that. If you’re on Ubuntu, swap the lib path to match the Ubuntu location.
When Things Go Wrong
“No Certificates Found” — check that pcscd is running (systemctl status pcscd), verify your card is detected (opensc-tool -l), and make sure the PKCS#11 module is actually loaded in your browser.
“Card Not Detected” — try another USB port, run lsusb to see if the reader shows up at all, and restart pcscd. I’ve also seen cases where a USB power management setting puts the port to sleep — disable USB autosuspend if you’re on a laptop.
“PIN Incorrect” when you know it’s right — this one is maddening. Clear your browser cache and certs, pull the card out and reinsert it, and restart pcscd. If it persists, your card’s PIN retry counter might be close to lockout — check with your ID card office before burning your last attempt.
Pro Tips
Use pkcs11-tool --list-slots to verify your card is communicating properly. Firefox ESR is more stable for CAC use than the regular release channel — fewer updates means fewer things breaking your security module config. And keep your opensc and pcsc-lite packages updated; the developers actively fix compatibility issues with newer card types.



Subscribe for Updates
Get the latest cac readers.com updates delivered to your inbox.
We respect your privacy. Unsubscribe anytime.